Bonjour,
Merci pour ton aide car là je galère et tourne en rond et je ne vois pas ce qui cloche.
Pour répondre à tes questions, voici ce que j'ai :
- Version Debian : 8.3
- Version Nginx: 1.9.11
Fichier ou sont définis les chemins des certificats (rutorrent.conf):
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
|
server {
## redirection url ##
listen 80;
server_name mydomaine.com www.mydomaine.com;
## redirection permanant HTTP: vers HTTPS: ##
rewrite ^ https://$server_name$request_uri? permanent;
## inclure pages erreurs ##
# include /etc/nginx/conf.d/error_pages.conf;
}
server {
listen 443 default_server ssl http2;
server_name mydomaine.com www.mydomaine.com;
index index.html index.php;
charset utf-8;
client_max_body_size 10M;
## Début ##
## ssl on;
## ssl_certificate /etc/ssl/nginx/mydomaine.com.crt-unified;
## ssl_certificate_key /etc/ssl/nginx/server.key;
## ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
## ssl_ciphers "EECDH+AESGCM:AES128+EECDH:AES256+EECDH";
## ssl_prefer_server_ciphers on;
## ssl_ecdh_curve secp384r1;
## ssl_session_cache shared:SSL:10m;
## ssl_session_timeout 10m;
## ssl_stapling on; ##
## ssl_stapling_verify on; ##
##################### Connexion Certificats SSL #########################
## ssl on;
## ssl_certificate /etc/ssl/nginx/Certificats/certif_mydomaine.com.crt-unified;
## ssl_certificate_key /etc/ssl/nginx/cles_privees_rsa/clePrivee.key;
## ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
## ssl_ciphers "EECDH+AESGCM:AES128+EECDH:AES256+EECDH";
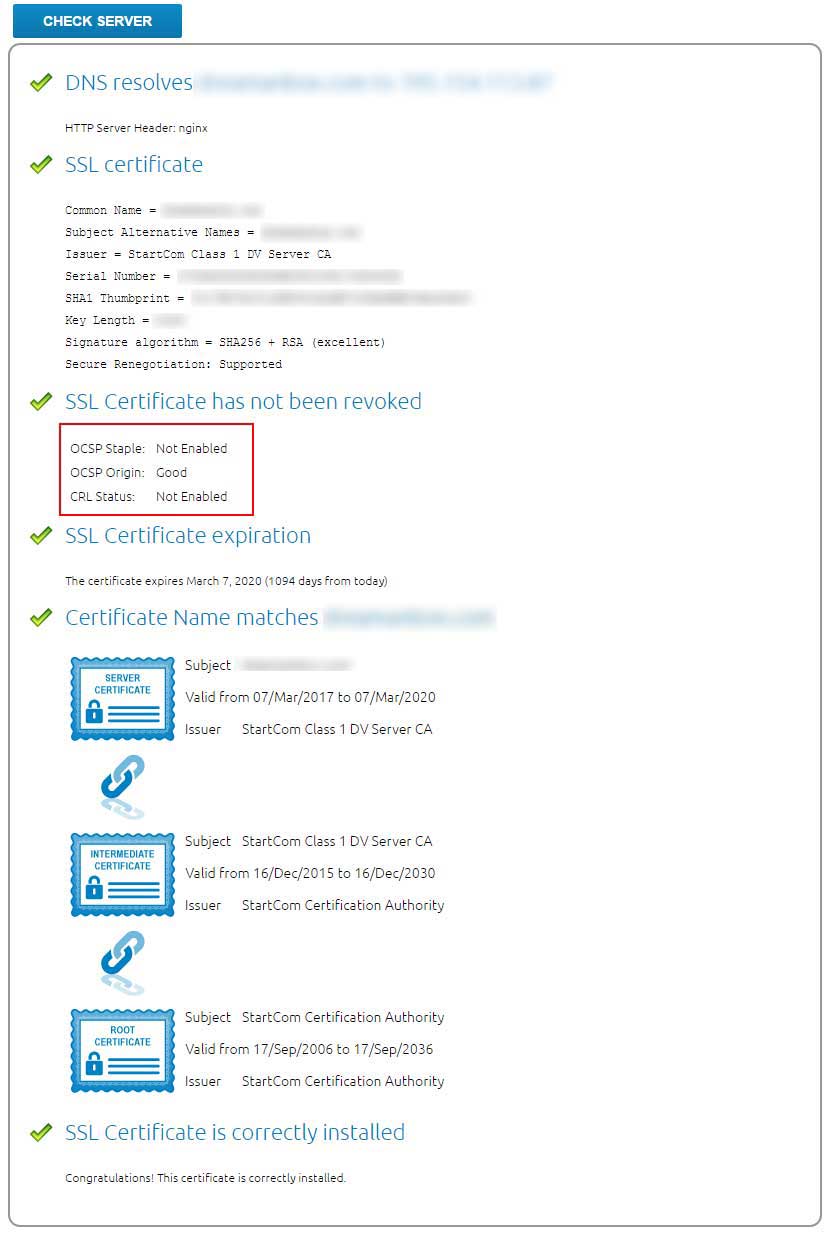
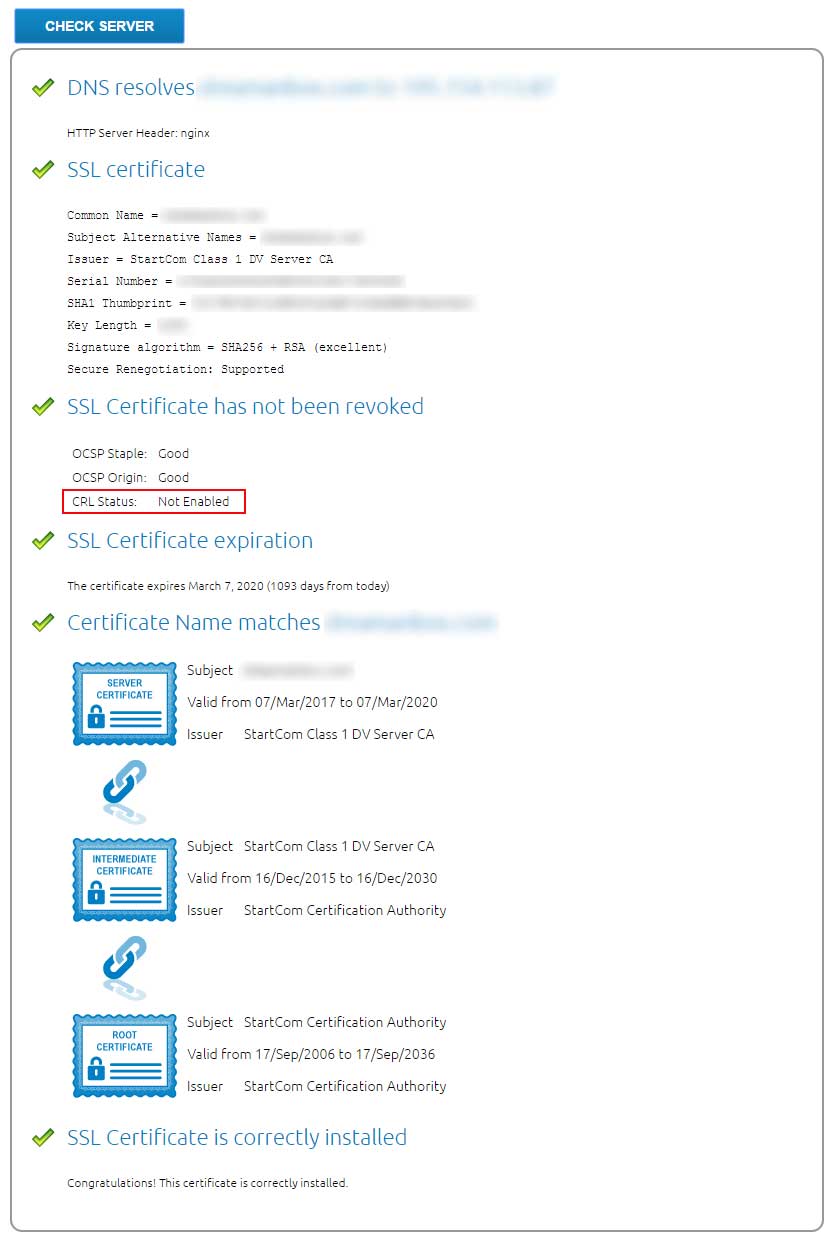
## Vérification OCSP Stapling validité Certificat SSL via StartCom ##
## ssl_stapling on;
## ssl_stapling_verify on;
## ssl_trusted_certificate /etc/ssl/nginx/Certificats/certif_mydomaine.com_ocs.pem;
ssl on;
ssl_certificate /etc/ssl/nginx/certif_mydomaine.com.crt-unified;
ssl_certificate_key /etc/ssl/nginx/clePrivee.key;
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
ssl_ciphers "EECDH+AESGCM:AES128+EECDH:AES256+EECDH";
## Vérification OCSP Stapling validité Certificat SSL via StartCom ##
ssl_stapling on;
ssl_stapling_verify on;
ssl_trusted_certificate /etc/ssl/nginx/certif_mydomaine.com_ocs.pem;
## Test ##
## ssl_trusted_certificate /etc/ssl/certs/ca.crt;
## ssl_trusted_certificate /etc/ssl/nginx/sca.server1.crt;
## ssl_trusted_certificate /etc/ssl/certs/ca-certificates.crt;
## ssl_trusted_certificate /etc/ssl/nginx/ca-certs.pem;
## SSLCACertificateFile /etc/ssl/nginx/ca-certs.pem;
## SSLUseStapling on
## Fin ##
resolver 8.8.4.4 8.8.8.8 valid=300s;
resolver_timeout 10s;
add_header X-Frame-Options "SAMEORIGIN";
add_header X-Content-Type-Options "nosniff";
## Fin ##
## inclure pages erreurs ##
include /etc/nginx/conf.d/error_pages.conf;
# On a neutralisés les lignes SSL et l'include ci-dessous car ajourt script ci-dessus
## ssl_certificate /etc/nginx/ssl/server.crt; ##
## ssl_certificate_key /etc/nginx/ssl/server.key; ##
# include /etc/nginx/conf.d/ciphers.conf; ##
access_log /var/log/nginx/rutorrent-access.log combined;
error_log /var/log/nginx/rutorrent-error.log error;
# error_page 500 502 503 504 /50x.html;
# location = /50x.html { root /usr/share/nginx/html; }
# auth_basic "seedbox";
auth_basic "mydomaine";
auth_basic_user_file "/etc/nginx/passwd/rutorrent_passwd";
location = /favicon.ico {
access_log off;
log_not_found off;
}
## début config accueil serveur ##
location ^~ / {
root /var/www/base;
include /etc/nginx/conf.d/php.conf;
include /etc/nginx/conf.d/cache.conf;
satisfy any;
allow all;
}
## fin config accueil serveur ##
## début config proxy ##
location ^~ /proxy {
root /var/www;
include /etc/nginx/conf.d/php.conf;
include /etc/nginx/conf.d/cache.conf;
}
## fin config proxy ##
## début config rutorrent ##
location ^~ /rutorrent {
root /var/www;
include /etc/nginx/conf.d/php.conf;
include /etc/nginx/conf.d/cache.conf;
location ~ /\.svn {
deny all;
}
location ~ /\.ht {
deny all;
}
}
location ^~ /rutorrent/conf/ {
deny all;
}
location ^~ /rutorrent/share/ {
deny all;
}
## fin config rutorrent ##
## début config munin ##
location ^~ /graph {
root /var/www;
include /etc/nginx/conf.d/php.conf;
include /etc/nginx/conf.d/cache.conf;
}
location ^~ /graph/img {
root /var/www;
include /etc/nginx/conf.d/php.conf;
include /etc/nginx/conf.d/cache.conf;
error_log /dev/null crit;
}
location ^~ /monitoring {
root /var/www;
include /etc/nginx/conf.d/php.conf;
include /etc/nginx/conf.d/cache.conf;
}
## fin config munin ##
## début config seedbox-manager ##
location ^~ /seedbox-manager {
alias /var/www/seedbox-manager/public;
include /etc/nginx/conf.d/php-manager.conf;
include /etc/nginx/conf.d/cache.conf;
}
## fin config seedbox-manager ##
## config utilisateurs ##
location /USER1 {
include scgi_params;
scgi_pass 127.0.0.1:5001; #ou socket : unix:/home/username/.session/username.socket
# auth_basic "seedbox";
auth_basic "mydomaine";
auth_basic_user_file "/etc/nginx/passwd/rutorrent_passwd_user1";
}
location /USER2 {
include scgi_params;
scgi_pass 127.0.0.1:5003; #ou socket : unix:/home/username/.session/username.socket
# auth_basic "seedbox";
auth_basic "mydomaine";
auth_basic_user_file "/etc/nginx/passwd/rutorrent_passwd_user2";
}
} |
Pour ce qui concerne la génération d'un certificat letsencrypt je vais voir cela, pour le moment je te donne ce que j'ai fait pour le certificat OCSP
Comment j'ai fait mon certificat full_chain.pem (qui se nome pour moi : certif_mydomaine.com_ocs.pem)
Puis j'ai concaténé mon certificat "certif_mydomaine.com.crt" et "cassha2.pem" en certificat unifier
cat certif_mydomaine.com.crt ca-sha2.pem > certif_mydomaine.com.crt-unified
J'ai dans un premier temps converti mon certificat "certif_mydomaine.com.crt" en certif_mydomaine.com_ocs.pem
openssl x509 -in certif_mydomaine.com.crt -out certif_bis_mydomaine.com_ocs.pem -outform PEM
Puis j'ai créer mon certificat unifier (full_chain.pem) que j'ai nomé "certif_mydomaine.com_ocs.pem"
cat certif_mydomaine.com.crt-unifie intermediate.pem > certif_mydomaine.com_ocs.pem
Je ne suis pas certain que cela soit correct !?









 Répondre avec citation
Répondre avec citation

Partager